In case you aren't inclined to read this post through and through, despite the beauty of its prose, here's the bottom line: Spearphishers cannot easily spoof a digitally signed message; so you should enable default digital signing of messages by all of your users to prevent spearphishing attacks.
Recently a friend told me about a security breach at his company. The breach was a textbook spearphishing attack. A member of the accounting department received an email message that purported to be from the company CEO. In the message, the “CEO” directed the recipient to wire umpteen thousands of dollars to a certain bank account. The email arrived late Friday afternoon and urged the recipient to wire the money “before close of business today”. The CEO was, of course, not around, so could not be reached to verify. The recipient bookkeeper did as directed and the company never saw the money again.
Recently a friend told me about a security breach at his company. The breach was a textbook spearphishing attack. A member of the accounting department received an email message that purported to be from the company CEO. In the message, the “CEO” directed the recipient to wire umpteen thousands of dollars to a certain bank account. The email arrived late Friday afternoon and urged the recipient to wire the money “before close of business today”. The CEO was, of course, not around, so could not be reached to verify. The recipient bookkeeper did as directed and the company never saw the money again.
Even more recently (because it's tax season, I suppose) I read that someone has been very successfully using spearphishing messages to trick companies into sending their employees' W-2 forms to the spearphisher. This spearphisher has succeeded so far in collecting some 120,000 W-2 forms from a number of organizations.
It occurred to me that if the victim companies used IBM Notes Mail they could easily have thwarted these spearphishing attacks.
Phishing attacks in general are a type of social engineering attack in which the attacker blasts a deceptive email out to as many recipients as possible, hoping to trick some of the recipients into responding in a way that will enable the attacker to rip off the respondent in some way. Spearphishing attacks are phishing attacks aimed at a single recipient. The email (or other attack vector) is finely tuned to trick the recipient into trusting the sender and responding positively. The email typically purports to be from a trusted, authoritative executive within the recipient’s organization; the email may direct the recipient to send money to some bank account and do it immediately because time is of the essence, as in my first example. Or, as in my second example, the goal may be to get the recipient to give away confidential information such as, oh, I don’t know, how about: The W-2 forms of every one of the organization’s employees!
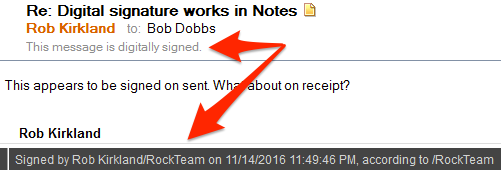
The feature of Notes that could have prevented these spearphishing attacks is digital signing of documents. IBM Notes for decades now has included a feature permitting senders to sign outgoing messages digitally. This is not a “written” signature at the bottom of outgoing messages, but rather an encrypted hash of the message that accompanies the message and enables the recipient to verify that 1) the message really came from the purported sender and 2) the content of the message was not altered en route to the recipient. When the recipient of the message opens it, Notes verifies the integrity of the hash and assures the recipient that the message is genuine. In the message header it displays “This message is digitally signed." In the Status Bar (bottom of the window) it briefly displays "Signed by <sender’s fully distinguished name> on <date> <time>, according to <certifier name>”.
A spearphisher could not easily spoof such a message because to do so he would have to obtain the sender’s private key, which only exists in the sender’s Notes user ID file. The spearphisher would have to obtain a copy of the purported sender’s ID file and learn its password (or, even harder, obtain a certifier ID and learn its password). That is, he would have to compromise both parts of a Notes user’s two-factor security. Not impossible, but not an easy thing for a total and remote stranger to pull off.
Digital signing of messages has been available in Notes since at least 1993. But it is voluntary by default. Notes users have to check a box to digitally sign any message before sending it. (They can check another box to digitally encrypt the message, too, if they want.) As you might guess, in most organizations hardly anyone ever checks the boxes or has any clue about why they might want to do so.
What Notes organizations can do (and should do soon, because spearphishers are clearly getting really good at their craft) is enable digital signatures by default, so that messages are digitally signed unless the sender turns off the feature.
First, of course, Notes administrators should notify their users that they will enable this feature.
Before that, though, and most importantly of all, Notes admins should educate their users so that
First, of course, Notes administrators should notify their users that they will enable this feature.
Before that, though, and most importantly of all, Notes admins should educate their users so that
- The users become appropriately paranoid about responding to mail that asks them to do potentially problematic things.
- The users know why digital signing is important.
- The users know that they should always look for the notice that the message is digitally signed before assuming a message from a purported Notes user is genuine.
And all of that being said and done, and now that the users know what to expect, what to do, and why it's important, the admins should enable default digital signing of Notes mail.
Enabling default digital signing of messages is very easy or moderately easy depending on a number of factors. Enabling it is very easy if all of an organization’s mail users use Notes to send and receive mail, and the only mail the organization is concerned about protecting with digital signatures is internal mail. An admin sets a particular field in a policy and applies the policy to the target users. Done.
Enabling default digital signing of messages is moderately easy if users also use Web browsers or non-Notes (POP, IMAP, IMSMO) mail programs or mobile devices to send and receive mail, because you can’t enable default digital signatures in non-Notes clients by policy. Rather, you have to convince users to enable it as a default in their user preferences. (That pretty much means that you really must educate your users in the importance of digital signatures, and not just pay lip service to it.) And you have to make sure that their ID files have either been merged into their mail databases or reside in an ID Vault. (But if your non-Notes mail users' mail resides on IBM cloud-based mail servers, their IDs must reside in the cloud-based ID Vault; merging their ID into their mail database won't be sufficient.)
Finally, if you also want to give users the option to sign messages addressed to recipients whose mail does not reside on Domino servers, the implementation process becomes not so easy at all. I'll be happy to discuss the complications involved in that process if either you or my other reader expresses interest in reading about it. But for now, I'll leave this discussion here:
- Educate management, HR, and your users about the dangers of spearphishing and how to cope with it.
- For your Notes mail users, use policies to enable default digital signing of messages to other Notes users.
- For your non-Notes, Domino-based mail users who have Notes IDs, encourage them strongly to enable the preference to sign outgoing mail by default. And get their Notes IDs merged into their mail databases or an ID Vault.
- For your non-Notes, Domino-based mail users who do not have Notes IDs, re-register them to generate Notes IDs for them.
- If you have non-Domino email users (Exchange, O365, Google, whatever), take two aspirin and call me in the morning.